DDoS Protection for SME Servers: Practical 2026 Guide
How DDoS attacks work, why SME servers are frequent targets, and which protection measures make sense in 2026.
DDoS attacks are often described as a problem for large brands, banks, or public services. That is misleading. SMEs are hit too, especially when they rely on one exposed server, one application endpoint, or one critical IP with no buffer around it.
Why SMEs are targeted
Attackers do not always choose targets for prestige. They often choose them for convenience:
- exposed public services
- weak upstream filtering
- predictable network layout
- poor visibility on abnormal traffic
A small business does not need to be famous to be disrupted. It only needs to be reachable and fragile.
What a DDoS attack actually does
A DDoS attack overwhelms a service by flooding it with traffic or requests until users can no longer reach it. The impact may affect:
- website availability
- VPN endpoints
- API services
- remote desktop gateways
- customer portals
The business effect is usually simple: downtime, support chaos, and loss of trust.
The main categories
Volumetric attacks
These try to saturate bandwidth with high traffic volume.
Protocol attacks
These target network or transport behavior, exhausting state tables or infrastructure capacity.
Application-layer attacks
These focus on HTTP or app logic, sending many requests that appear legitimate but consume server resources.
SMEs often underestimate the third category because the traffic may look “normal” at first glance.
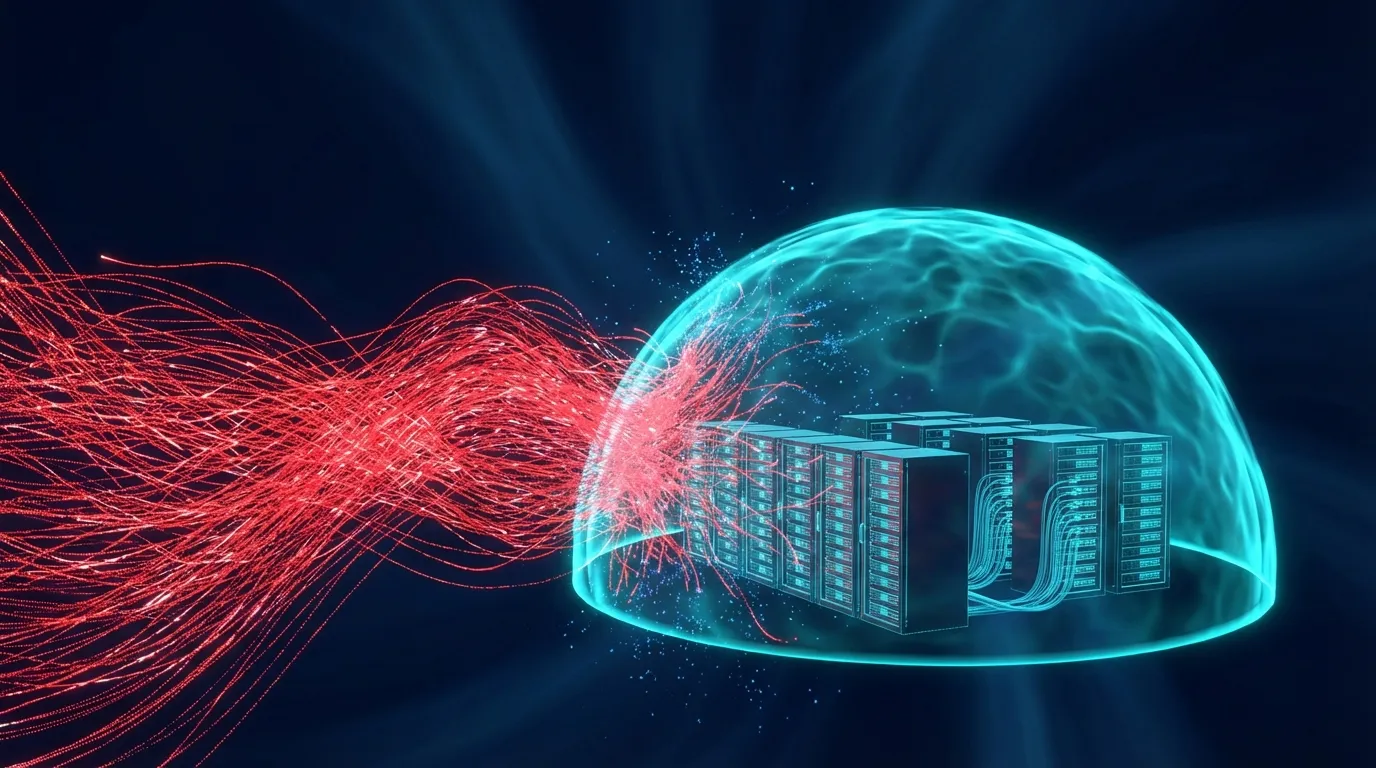
What practical protection looks like
For most SMEs, DDoS resilience comes from layers, not one product:
- a controlled perimeter with a managed firewall
- rate limiting and filtering
- reduced exposure of administrative services
- upstream mitigation where needed
- clear visibility into unusual traffic patterns
The worst design is a directly exposed business server with no separation between public traffic and management traffic.
DDoS and business continuity
DDoS protection is not only about blocking packets. It is about preserving service continuity. That means asking:
- Which services must remain reachable?
- Which services can be restricted quickly?
- Who decides when to trigger mitigation or temporary containment?
Without those answers, technical controls alone are not enough.
Conclusion
For SMEs, the goal is not to build an enterprise anti-DDoS war room. It is to avoid becoming an easy disruption target. That starts with reducing exposure, separating critical services, and using managed controls that make abnormal traffic visible before it turns into downtime.